Conferences & Presentations
Sneak Peak at a New SANS Course: InfoSec Risk Management
SANS is launching a new course, MGT 442: Information Security Risk Management, this September and I will be presenting a free sneak peek at this new course during an evening event at SANS Boston.
Risk Business
Speaker: Evan Wheeler
Date/Time: Wednesday, August 4, 8:00pm - 9:00pm
In many IT security programs, information security is forced on the organization. This approach often creates resistance leading to limited success in actually securing the environment. The security function needs to instead work collaboratively with the business units to identify and prioritize the real threats to core business objectives.
In this talk, we will demonstrate how to develop your own risk criteria by analyzing some recent vulnerability notifications. By the end of the hour, attendees will know how to analyze a new vulnerability report for the distinguishing characteristics that would make it a critical weakness for some, but a moderate concern for you.
By shifting the focus away from blindly applying industry standards across the board and minimal compliance with regulations, the security function can help to identify and address the real risk exposures that are most likely to impact the organization.
Location
Hyatt Regency Boston
One Avenue de Lafayette
Boston, Massachusetts, USA 02111
Telephone: (617) 912-1234
Website: http://regencyboston.hyatt.com/hyatt/hotels/index.jsp
RSA Conference 2010 - Security Decoded
RSA Conference continues to play an integral role in keeping security professionals across the globe connected and educated. The focus on cyberthreats grows each day and RSA Conference is the educational and training environment to prepare you to meet these challenges.
Evan will be moderating a panel session this year on the topic of Building an Information Security Risk Management program, and he will also be facilitating a Peer2Peer session for aspiring security consultants. Details about each of these sessions follow:
 Check out my session:
Check out my session:
Risk Management: The Next Evolution in Security
03/02/10 | Session Code: STAR-108
If organizations hope to survive the ever-changing threat and regulatory landscapes, they need to develop and effectively use a well thought out risk-based information security framework. This expert panel of information security leaders will discuss their own approaches to developing an Information Security Risk Management program across many industries. Learn the most critical ingredients and specific steps to get a successful program off the ground while avoiding common pitfalls.
Listen online to Evan Wheeler give a brief recap of this popular panel discussion as part of the RSA Conference 2010 - Podcast Series.
As a follow up to this session, the panelists have started a new group on LinkedIn to discuss issues and ideas for building information security risk management programs. To join this group, log into LinkedIn and search the Groups Directory for Information Security Risk Management Program Development.
Jeff Bardin has posted 7 Risk Management survey questions on LinkedIn. The results of these surveys were shared during this panel discussion at RSA 2010. You can view the results by following the links on Jeff's blog, The Brave New World of InfoSec, on CSO Online.
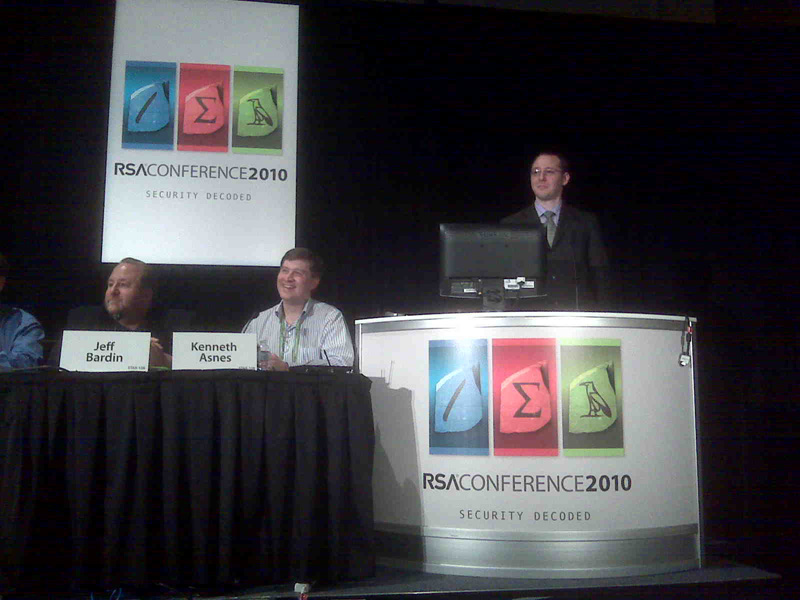
From Left to Right: Jeff Bardin, Ken Asnes, and Evan Wheeler
For a description of Evan Wheeler's background, see the About the Author page.
Jim Routh has over 20 years of experience in information technology and information security as a practitioner, management consultant and leader of IT Risk functions for global firms. Jim is the former CISO for KPMG LLP, The Depository Trust and Clearing Corporation (DTCC) and American Express. Mr. Routh was selected the 2007 Information Security Executive of the year for the Northeast. He was awarded the BITS Leadership Award.
Jeff Bardin has held Top Secret clearances while working for the U.S. Government (USAF/NSA) and also served as an Armored Scout Platoon Leader. Bardin was awarded the 2007 RSA Conference award for Excellence in the Field of Security Practices. The Bardin-led security team from Hanover Insurance also won the 2007 SC Magazine Award for Best Security Team. He holds CISSP, CISM and NSA IAM certifications, a B.A. in Middle East Studies and Arabic Language and an M.S. in Information Assurance.
Ken Asnes received his BSEE and MBA from Northeastern University and currently holds CISSP and GFCA certifications. He has over 15 years in the information security field as a developer and as a manager.
Denny Dean is Chief Information Security Officer at The Hanover Insurance Group. He has over 20 years experience facing the challenges of IT governance and delivering information security solutions to industry leading entities including the United States Air Force, Harvard University, Lucent Technologies, AON, Bank of America, and Staples. Co-recipient of the "Security Team of the Year" award, 2007 - SC Magazine. His credentials include the CISM, CISSP, CISA and ITIL certifications.
 Check out my session:
Check out my session:
From Security Insider to Security Consultant
03/03/10 | Session Code: P2P-205B
Given recent economic conditions, many security professionals are turning to consulting to get by, but do you really know how to sell yourself as a consultant, answer an RFP, run a scoping meeting, or define the rules of engagement? Especially for the professionals who are going out on their own as independent consultants, it is essential that you know how to properly scope a project and cover your own liability. Join your peers to discuss the successes and challenges of security consulting.
A Crash Course in Security Consulting
Current economic conditions are forcing many security professionals to turn to consulting to get by, but do you really know how to sell yourself as a consultant, answer an RFP, or run a scoping meeting? Especially for the professionals who are going out on their own as independent consultants, it is essential that you know the tips and tricks to be successful. Join us for a crash course where you can get your questions answered by expert consultants in the field:
|
Space is limited, so please RSVP to coins@sans.org.
Community SANS Boston Fall 2009 is offering a local session of the popular SEC 501 Advanced Security Essentials - Enterprise Defender course taught by certified instructor Eric Conrad.
 Location
Location
Courtyard by Marriott Woburn/Boston North
700 Unicorn Park Dr.
Woburn, MA
Wednesday, October 28, 2009
Time: 6:30-9:00 (with Beer and Appetizers)
Presenters
Eric Conrad - Certified SANS Instructor Eric Conrad's career began in 1991 as a Unix sysadmin for a small oceanographic communications company. He gained experience in a variety of industries, including research, education, power, Internet, and healthcare, and has worked with companies such as Mitsubishi Electric Research Labs, Boston University, The Open Group, Navipath, and Caritas Christi Health Care. He is now an independent information security consultant focusing on intrusion detection, incident handling, and penetration testing. In addition to the CISSP, he holds the prestigious GIAC Security Expert (GSE) certification as well as the GIAC GPEN, GCIH, GCIA, GCFA, GAWN, GSEC certifications. He is a contributing author to SANS HIPAA Security Implementation.
Robert Emerson - Robert Emerson is Chairman and co-founder of Business Training and Consulting Institute (BTC Institute), a supplier of innovative training products and services for rapidly conveying business skills. Having successfully sold to the Global 1000 many seven-figure deals for solutions comprised of products, services and ideas, Robert Emerson has experienced strong success in business-to-business sales. Robert often mentions the saying: All business is sales. Over three decades, he's been recognized as a top producer, whether in new business sales, existing account growth or turnaround successes. Robert has lead 22-person sales teams and 42-person marketing units. He has made presentations to potential investors leading to the acquisition of one company. Throughout his career, colleagues have remarked that Robert has at his core the characteristics of an educator, teacher, mentor, coach and advisor. It was with this background that he was attracted to the value proposition for BTC Institute: Just share with others all the secrets of what to say and do to be more successful.
Evan Wheeler - For a description of Evan Wheeler's background, see the About the Author page.
This presentation is part of the SANS Community Of Interest for Network Security (COINS) program. which was developed as a way of supporting local professional information and cyber security groups by offering SANS instructors and SANS content to local InfoSec Chapters all over the U.S and Canada. They support associations like: Information System Security Association (ISSA), Information Systems Audit and Control Association (ISACA) , High Tech Crimes Association (HTCIA), Infragard and others. For more information on how they can work with your organization, please contact Sonya Goulet, Director of the COINS program (http://www.sans.org/coins/). This session contains excerpts of the SANS SEC 560 Network Penetration Testing & Ethical Hacking course.
CSI Conference 2009: Security. Strategy. Success.
The organizations that thrive today are those that effectively manage and address an increasing number of security challenges: mobility security, outsourcing leaks, customer data privacy, increasing regulatory compliance issues, the latest cybercrime threats and more.
CSI 2009 will focus on these topics, as well as show you how to proactively build security into the business plan, manage risk and make decisions regarding the new technologies such as cloud computing, virtualization and Web 2.0.
Gaylord National Resort and Convention Center
201 Waterfront Street
National Harbor, MD 20745
Phone: 301.965.2000
Check out my session:
Risk Management Summit: Why Risk Management?
Monday October 26th, 2:00pm - 5:30pm
Parts I - III
| Speakers | ||
|
Ronald Woerner John Pironti James Tomlinson Wilco van Ginkel Evan Wheeler Thomas Peltier |
Security Compliance Manager, TD Ameritrade ThinkTech Chief Information Risk Strategist, Archer Technologies LLC Senior Security Strategist, Verizon Business Senior Consultant, Verizon Business Information Security Team Lead, Omgeo (A DTCC | Thomson Reuters Company) President, Thomas R. Peltier Associates, LLC |
|
Presentation Abstracts
Why Risk Management?
Many organizations are moving away from traditional information security programs and instead adopting an information risk management approach to security. Easier said than done. The Risk Management Summit kicks off with all summit speakers identifying the most challenging, confusing and contentious risk issues - like what exactly is risk management, and how do you balance the fluidity of risk and the rigidity of compliance?
Laying the Groundwork: Classifying Assets and Identifying Stakeholders
The Risk Management Summit continues by pulling apart and putting back together the nuts and bolts of every risk management program. Learn how to build a risk management program from the ground up -- starting by asking "what best serves the business" then doing a thorough inventory and classification of all your organization's information assets.
Choosing a Risk Management Methodology
Once you've laid the groundwork for your organization's risk management program, what comes next? The Risk Management Summit concludes with the speakers and attendees openly debating over the best answers to difficult questions posed earlier, and discussing the best technological and management solutions to these challenges.
Topic - Risk Management
SANS Webcast: Changing the Way We Manage Vulnerabilities & Patching
SANS is happy to bring you the latest in our complimentary series of Webcasts. Join us on Tuesday, October 20 at 12:00 PM as SANS present this special webcast sponsored by Rapid7. This is the first of what I hope to be a series of webcasts on various topics related to Information Security Risk Management.
Register for this free Webcast
Changing the Way We Manage Vulnerabilities & Patching
Time: Tuesday, October 20 at 12:00 PM EDT (1600 UTC/GMT)
Webcast Overview
If you are a resource administrator, then you probably spend too much time responding to new vulnerability reports and patching systems. For the security folks, you probably spend too much of your time tracking down the status on remediation and trying to qualify new vulnerability notifications. So how can we manage this better? This session will focus on how to take vendor and industry reports of new vulnerabilities in software/hardware, and analyze the risk to your own organization. With limited time and resources, you can't patch everything on day 1, so how do you determine which alerts are actually critical for your environment?
The answer is to develop a risk model that takes into account the particulars of your environment. We will demonstrate how to develop your own risk criteria for severity and likelihood by analyzing some recent vulnerability notifications. By the end of this session, attendees will know how to analyze a new vulnerability report for the distinguishing characteristics that would make it a critical weakness for some, but a moderate concern for you. Armed with this knowledge, you can better focus your administrators' efforts.
Catch a preview of this webcast on Akibia's Practical Guide to Enterprise Technology blog site: Improving Vulnerability & Patch Management
Information Security Awareness Conference 2009
Introduction to Digital Investigations
Holyoke Community College is hosting the event on October 16th, 2009 at the Leslie Phillips Forum. The purpose of this conference is to focus attention on cyber security. With the steep rise in e-discovery requests and other internal investigations involving technology, the need for digital forensic skills has never been higher. This session will cover investigation techniques ...
RSA Conference 2009
Architectural Risk Analysis
How do you validate the design of new applications before coding even begins? Do you have a formal methodology to assess the fundamental design of third-party applications or services? The key is defining an enterprise-wide approach to security architectural risk analysis. This expert panel will describe their experience implementing solutions in many of the most challenging environments ...
